Physical Access Control
Control every entry. Eliminate uncertainty. Real-time access tracking, permissions, and full audit visibility.
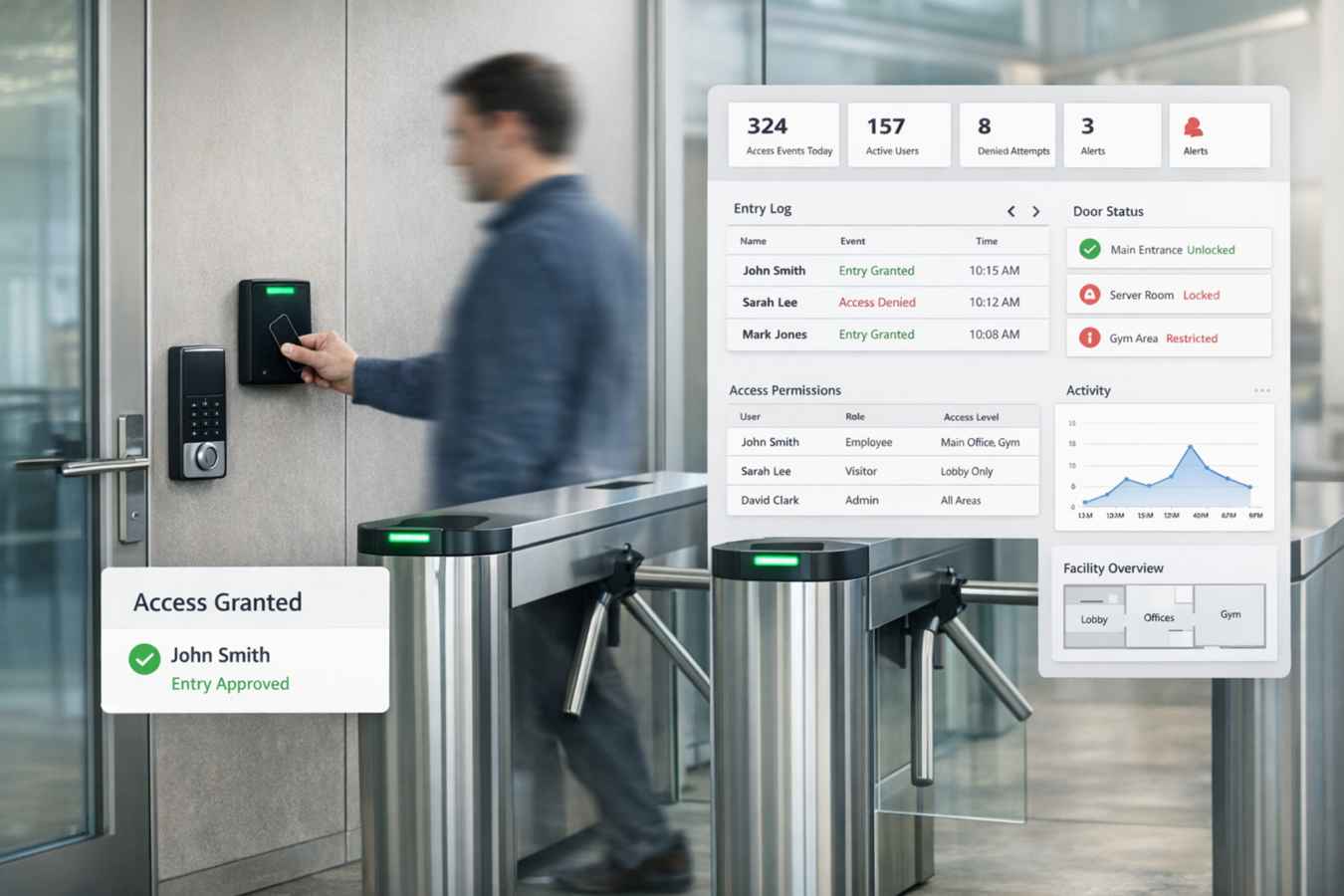
Centralize Access Permissions
Physical access control software ensures that every user’s access level is defined and traceable. Access governance becomes structured and enforceable.
Role-Based Permissions
Assign role-based access permissions across users.
Access Zones
Define access zones by location and facility.
Time-Based Restrictions
Set access permissions based on schedules and time windows.
Credential Management
Manage temporary credentials and badge assignments.
Access Tracking
Track credential assignments and user access activity.
Monitor Entry and Exit Activity
Visibility strengthens security. Every facility interaction is documented and searchable.
Entry & Exit Logs
Log all entry and exit events across facilities.
User & Location Tracking
Track access by individual user or facility location.
After-Hours Monitoring
Monitor access outside standard operating hours.
Access Attempt Reviews
Review failed or unauthorized access attempts.
Timestamped Records
Maintain detailed timestamped access logs.
Enforce Multi-Site Security Control
Organizations with distributed facilities require centralized oversight. Security remains consistent across locations.
Multi-Location Access Management
Manage access permissions across multiple facilities.
Cross-Site Permissions
Assign user permissions across different locations.
Centralized Dashboards
Monitor access activity through consolidated dashboards.
Department-Level Security Roles
Define security roles by department and function.
Provide Real-Time Security Visibility
Security teams need immediate insight into facility activity and access behavior.
- Real-time access dashboards
- User activity tracking
- Access attempt monitoring
- Location-based visibility
- Security event summaries
Support Compliance and Audit Requirements
Access records support compliance mandates and audit readiness.
- Maintain audit-ready access logs
- Track security policy enforcement
- Document access-related incidents
- Monitor credential expiration
- Generate compliance reports
Built Directly Into Salesforce
Physical access control becomes embedded into your operational system.
User Integration
User records connect directly to access permissions.
Real-Time Logs
Entry logs update instantly across the system.
Live Dashboards
Dashboards reflect live facility activity.
Governance Enforcement
Role-based permissions enforce structured security governance.
AI-Powered Security Monitoring
Security management becomes proactive with intelligent monitoring.
AI-Driven Security Intelligence
Your security strategy becomes data-driven.
Anomaly Detection
Detect unusual access patterns automatically.
Failed Attempt Alerts
Flag repeated failed access attempts.
After-Hours Risk Detection
Identify unusual after-hours access behavior.
High-Risk Zone Monitoring
Track access activity in sensitive areas.
Security Optimization
Improve response planning with predictive insights.
